Experience the Power of Productivity
Make your team 40% more efficient. Set up your account in just 2 minutes!
Get clear visibility into team activity, identify productivity trends, and make informed decisions to improve performance.
Track user activity on the go with Workstatus’s mobile app for seamless monitoring and insights anywhere.
Active users
Hours Tracked
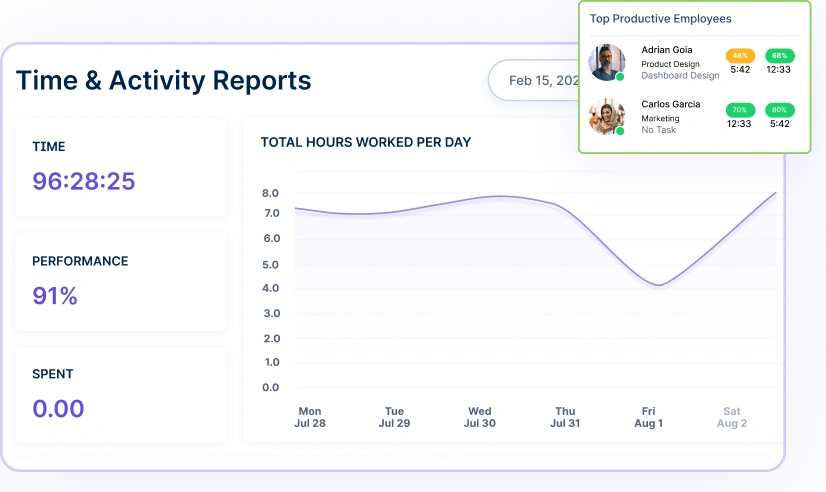
Track and optimize team performance with instant workforce analytics and actionable insights.
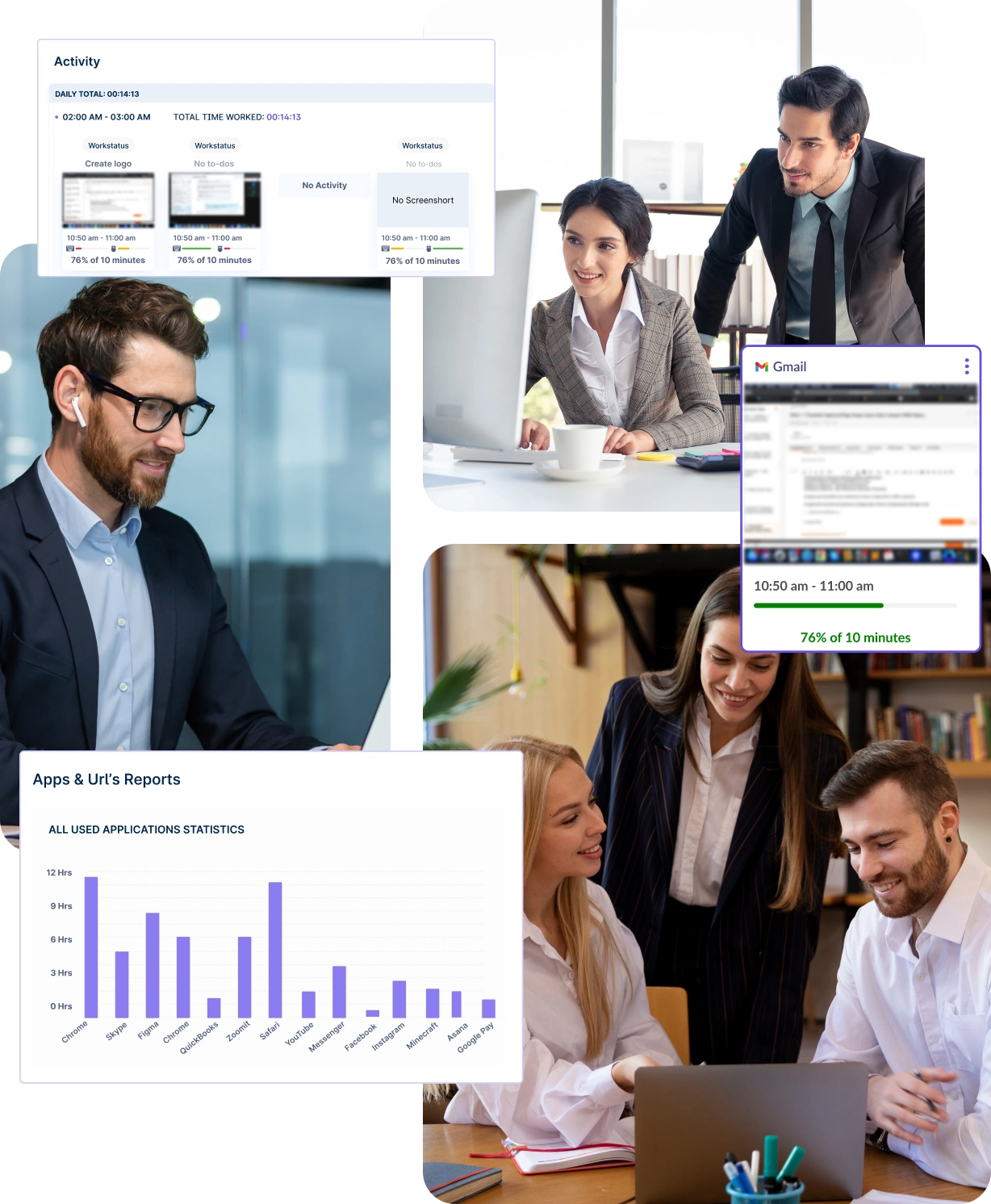
Track applications and websites employees visit during their workday to identify potential distractions and inefficiencies.
Gain real-time insights into employee activities through screenshots, ensuring transparency and accountability in your projects.
Give users complete control over their data with transparent, easy-to-use privacy settings.

Restrict data access to authorized personnel only, effectively safeguarding sensitive, confidential, and proprietary information.
Choose stealth mode to monitor user activity silently and discreetly without alerting employees, ensuring their behavior remains unaffected.

A multi-national marketing firm, boosted overall efficiency.
Increase Your Team Productivity
A Delhi-based startup achieved 30%+ increased ROI with Workstatus.
Enhance Your Business ROIEffortlessly maintain regulatory requirements with comprehensive tracking and reporting of all system interactions.
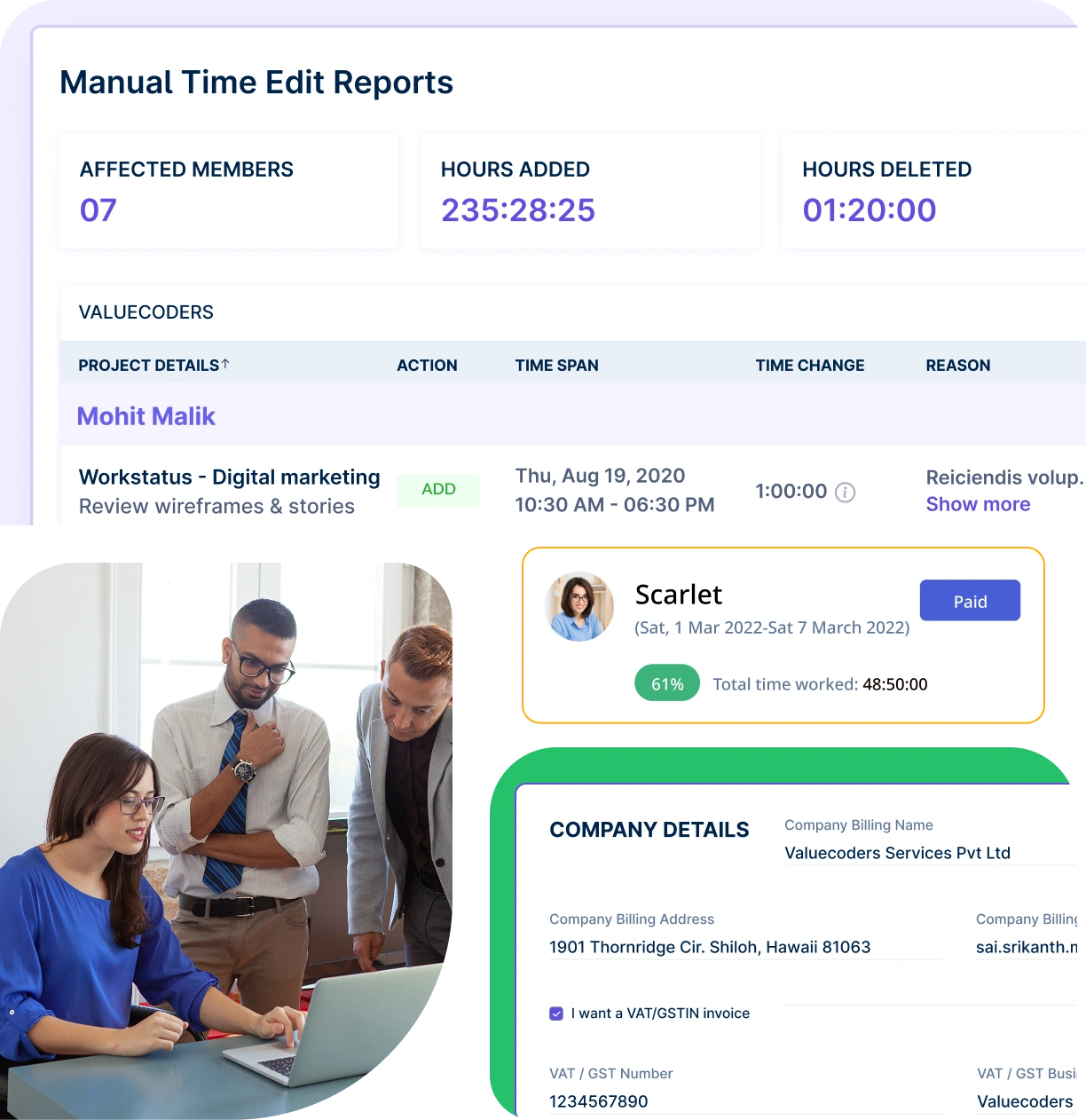
Keep detailed, accurate records of all user activities to facilitate comprehensive compliance audits and reporting with advanced employee monitoring.
Automatically monitor compliance with company rules, procedures, and regulations through detailed user activity data insights.
Monitor user activity across teams, ensuring productivity and accountability wherever your team works.
Capture activity, analyze performance, and grow productivity.
From IT to healthcare, retail to manufacturing, Workstatus adapts to meet your industry’s unique needs.



We provide clarity, no matter the industry, with:
Analyze and assess tools side by side to choose the best fit for your team’s needs and goals.
From time tracking to advanced analytics, Workstatus has everything your business needs to elevate operations.
Workstatus fits seamlessly into your existing tools, connecting time, tasks, and insights without changing how your teams work.
Tracking user actions on systems helps maintain visibility and accountability across workflows.
Organizations use tools to understand patterns, maintain security, and support performance improvement.
Using user activity monitoring software like Workstatus gives leaders clarity without constant manual checks.
It strengthens security and supports ethical operations.
The best user activity monitoring tools, like Workstatus, collect behavioral and system-use information to create work insights and security visibility.
A reliable employee monitoring software ensures accurate recording while keeping systems secure.
Accurate insights depend on precise tracking and reliable systems.
Modern platforms like Workstatus use automated logging to avoid errors.
Here’s how user activity monitoring ensures data accuracy:
Strong processing frameworks keep employee activity monitoring fast, reliable, and secure.
This helps reduce human error and ensures trust in recorded data.
Ethics matter when monitoring employee systems.
Transparency builds trust and keeps practices compliant.
Here are some ethical considerations in monitoring user activity:
Ethical user activity monitoring software like Workstatus supports teams instead of policing them and keeps transparency at the core.
Maintaining trust is as important as visibility. Tools should empower managers without invading personal space.
Here’s how monitoring tools can balance oversight with privacy:
Fair use and smart controls keep employee monitoring respectful and compliant.
Balanced oversight protects privacy while still supporting accountability.
Visibility into workflows helps optimize effort and remove work barriers.
Here’s how activity monitoring can improve productivity:
With user activity monitoring software like Workstatus, teams get insight, practice better habits, and improve performance over time.
We take your data security seriously. Workstatus implements advanced encryption protocols and follows stringent compliance guidelines to protect your information.

SOC 2 Type II attestation is our commitment to the highest standards of data security, privacy, availability, processing integrity & confidentiality.

Fully compliant with the General Data Protection Regulation (GDPR), we adhere to strict guidelines regarding the collection, storage, and processing of personal data.

Our ISO 27001 certification signifies adherence to international standards for information security management systems (ISMS).

We are dedicated to upholding the stringent requirements of the Health Insurance Portability and Accountability Act (HIPAA).
The user activity monitoring feature allows businesses to track employee productivity and ensure efficient use of work hours. With this tool, employers can monitor various metrics like application usage, website visits, and active time spent on tasks.
Key features include:
This helps businesses ensure transparency and accountability, leading to higher productivity. Workstatus’s activity monitoring feature is secure, private, and customizable for different business needs.
Workstatus enhances employee productivity by providing businesses with tools to track work hours accurately, prevent time theft, and monitor overall performance. This allows businesses to identify inefficiencies and provide necessary support or adjustments. The result is a more focused and productive workforce, helping you meet its goals more effectively.
Workstatus is designed with remote teams in mind, offering features that allow managers to track employee activity from anywhere. With its User Activity Monitoring, you can:
This transparency ensures that remote teams stay on track, work efficiently, and remain aligned with company objectives. With Workstatus, you can manage your remote workforce as effectively as in-house teams.
Yes, Workstatus prioritizes security and privacy when it comes to user activity monitoring. The screenshots captured are random and do not invade employee privacy. Additionally, the software:
This means you can track productivity while maintaining a respectful and secure working environment. Hubstaff ensures transparency and fosters trust between employers and employees.
Yes, Workstatus can track time spent on non-work apps and websites, helping businesses identify and minimize distractions. The user activity monitoring feature gives detailed insights, including:
By pinpointing these distractions, businesses can create strategies to improve productivity and focus. Workstatus allows you to manage these settings to ensure a balanced approach to monitoring employee activity.
Managing your workforce, projects, and reports gets simple & effective.
Managing your workforce, projects, and reports gets simple & effective.

Workstatus is highly rated on Trustpilot for reliability, ease of use, and workforce visibility.
Explore MoreTracking time is not enough. Identify up to 20–25% revenue leakage, improve utilization by 15%, and prevent costly overruns.